 We are under attack! Right now, the U.S. is the top target for external cyber attacks. But fear not! We have hardened ourselves against these- at least we’d like to think we have. So why are we still at risk? Any time we are looking at threats, we forget the number one threat to our company- internal employees.
We are under attack! Right now, the U.S. is the top target for external cyber attacks. But fear not! We have hardened ourselves against these- at least we’d like to think we have. So why are we still at risk? Any time we are looking at threats, we forget the number one threat to our company- internal employees.
A Harvard Business Review says that, “Insiders can do much more serious harm than external hackers can, because they have much easier access to systems and a much greater window of opportunity.” So what do you do to prevent users from hitting you where it hurts?Even though Greg from Accounting might seem harmless, it could be extremely easy for him to compromise a system (and we don’t even know it!). Greg could have a bad week, be disgruntled, and take it out on the company. Greg could be wondering the company website and stumble upon something he shouldn’t. He could accidentally delete something he shouldn’t because we haven’t assigned the proper permissions to users. Or we have administrative accounts that have been compromised because we use the same, easily guess-able password on several different websites.
To help you and your company be protected from possible malicious internal employees, StormWind has introduced a brand new course, “Securing Windows Server 2016” which maps to Microsoft Exam 70-744. This course will teach you how to harden your systems from employees like Greg and others.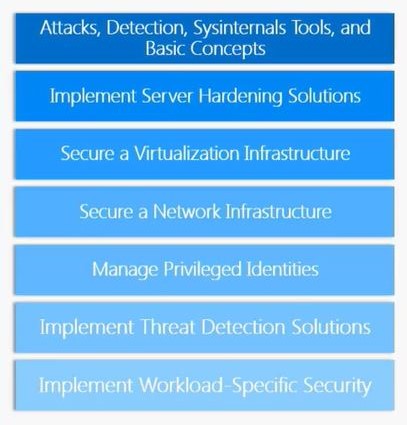 The course begins with detecting attacks and seeing what an actual attack may look. We will be using Sysinternals tools and “Assuming Breach” which is the new philosophy for hardening systems. You may have heard to never assume things (because you make an A** out of U and ME) but in this case, we need to assume that our network infrastructure, servers, and administrative level accounts have been penetrated.
The course begins with detecting attacks and seeing what an actual attack may look. We will be using Sysinternals tools and “Assuming Breach” which is the new philosophy for hardening systems. You may have heard to never assume things (because you make an A** out of U and ME) but in this case, we need to assume that our network infrastructure, servers, and administrative level accounts have been penetrated.
We need to assume that the consoles we use to try and do our administrative tasks have been compromised in order to learn how to harden them. That way if someone like Greg comes in and has compromised credentials, ability to run certain PowerShell commands, can infiltrate external information (etc.) we want to secure our systems to minimize the damage and let us know when/where/how the attack is happening.
if dealing with the day-to-day shenanigans of your users wasn’t enough, IT professionals also have to detect potential insider threats from your users’ behavior. We came up with 15 reasons why your users may screw up your network security. Download and share this ebook today! Doug brings over thirty years of experience in consulting, operations, network design and instruction, serving small office/home offices as well as global enterprises. As a technical instructor, Doug’s high energy, infectious enthusiasm and unmatched passion for training and “all things gizmo” leave students energized, excited and driven to devour complex technology and innovation.
Doug brings over thirty years of experience in consulting, operations, network design and instruction, serving small office/home offices as well as global enterprises. As a technical instructor, Doug’s high energy, infectious enthusiasm and unmatched passion for training and “all things gizmo” leave students energized, excited and driven to devour complex technology and innovation.
Known for getting the audience to do “the wave” at events, Doug was a featured speaker at Microsoft TechEd in Barcelona Spain on Virtual classroom training and has presented numerous times at Fortune 100 corporations like Microsoft and Apple. Wanna join his next class? Learn more here.

